Wan Optimization
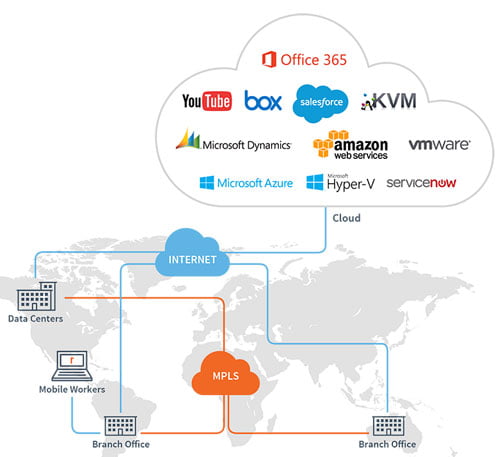
By combining network, application, and end-user performance metrics for deep visibility, IT can troubleshoot and fix problems before the user is impacted. Leveraging the solution’s application-aware approach, the most complete set of network services, and path selection based on intent-based, business-driven, global policies with local enforcement, you also have significantly improved control to enable business agility.
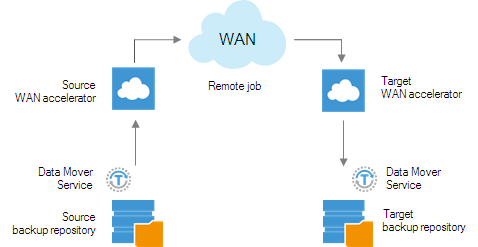
What is a WAN accelerator?
A WAN accelerator reduces the amount of data that needs to flow back and forth across the WAN by using caching and data compression techniques. Basically, a WAN accelerator works by caching duplicate files (or parts of files) so they can be referenced in the global cache instead of having to be sent across the WAN again. WAN accelerators effectively trade off network I/O for disk I/O, thus significantly improving the performance of data transfers over the network in situations when bandwidth is the primary bottleneck.
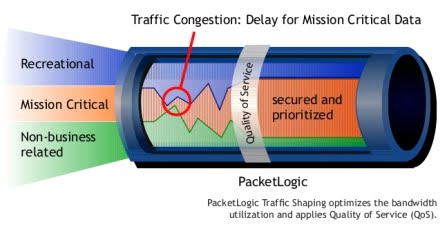
Traffic Shaping
Traffic shaping is about regulating the average rate of data transmission. Until the hosts send a certain limit rate of data, traffic shaping reduces congestion. This certain limit may be of importance while transferring the file but plays a vital role in the case of real-time data (audio, video, etc) transfer.
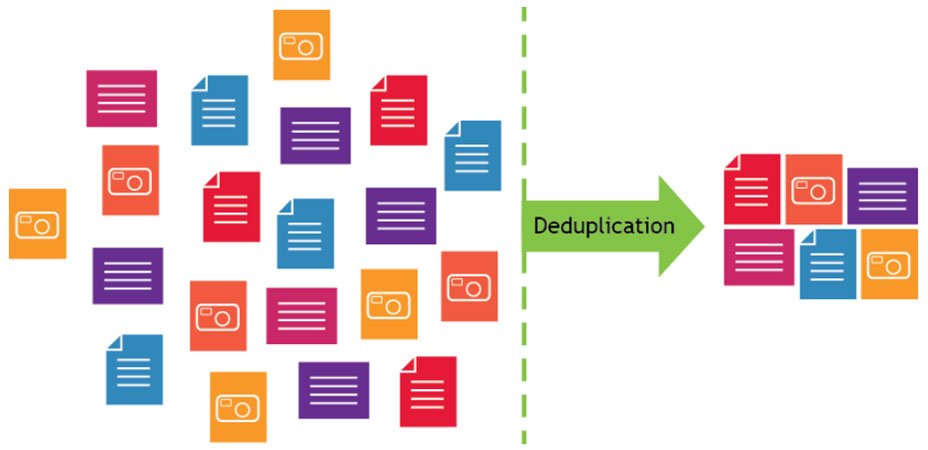
Data Deduplication
Deduplication is a computer industry term for “removing the duplicates,” and, as this strange word implies, it’s a process that examines a hard drive or storage system to find and remove duplicate files — effectively reducing the amount of storage required for a given set of data. The “reclaimed” storage is then available for additional data. The net effect of deduplication is to increase available capacity and perhaps forestall the need to buy additional capacity. It’s clearly a good green measure to take.
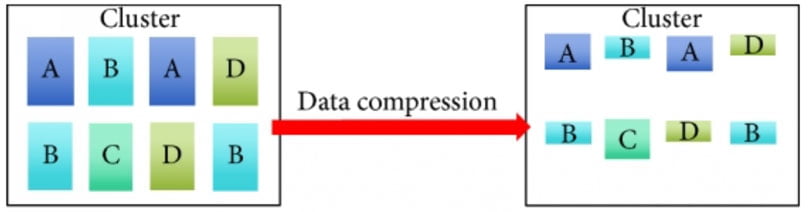
Data Compression
Is a reduction in the number of bits needed to represent data. Compressing data can save storage capacity, speed up file transfer, and decrease costs for storage hardware and network bandwidth.
Compression is performed by a program that uses a formula or algorithm to determine how to shrink the size of the data.
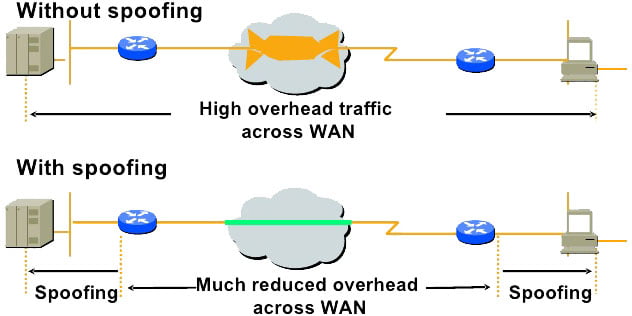
Protocol Spoofing
Protocol Spoofing is an essential part of data communications that helps to enhance performance. This technological aspect comes as an effective solution particularly in situations when an existing protocol is not adequately characterized by high error rates and long delays.
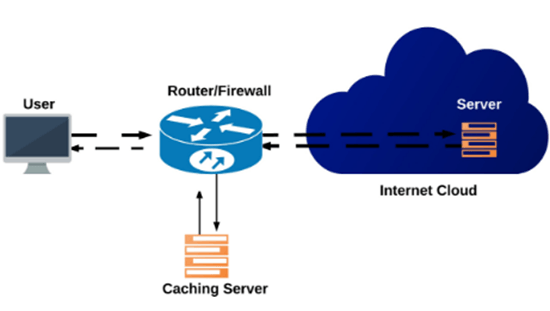
Data Caching
Caching servers have built-in intelligence to store the most recent and most frequently requested information, thus preventing future requests from traversing a WAN/Internet link unnecessarily.
Caching servers keep a timestamp of their last update to data. If the page timestamp has not changed since the last time a user has accessed the page, the caching server will present a locally stored copy of the Web page, saving the time it would take to load the page from across the Internet.
Benefits of WAN Optimization Solutions
- Deliver the best end user experience across the Hybrid WAN with accelerated performance of all applications.
- Resolve problems faster with improved IT visibility into application, network, and end-user experience.
- Gain greater control with a simplified, wizard-like approach that translates business intent into application-centric service policies and automatically derives all possible network path possibilities based on availability.